We’re back again with two exciting days of knowledge-sharing, networking, and insightful conversations. This year, stackconf found its home in the vibrant city of Berlin, and it’s a pleasure to be back! Bernd set the tone for the event by extending a warm welcome to our eager attendees, ready to dive into the thought-provoking talks lined up for the conference. With both familiar faces and newcomers among our speakers, this year’s event promises fresh perspectives and engaging discussions.
Here are a few of the talks that stood out for me today. You can find the other presentations from our speakers and their profiles on our homepage or in the event app.
Scaling a Collaboration Service like Nextcloud to 20 Million users with Frank Karlitschek.
The day began with a captivating talk by Frank on the exciting world of Nextcloud AI. Frank gave us a sneak peek into the next update, highlighting the seamless integration of AI tools. What’s unique about this integration is that it’s localized on your server, keeping your data secure. Frank’s talk covered a range of applications, from writing headlines and summarizing emails to generating images and transcribing speech to text. The promise of a Nextcloud assistant AI on the horizon adds to the anticipation of what’s to come.
Open-Source: Open Choice – A DevOps Guide for OSS Adoption with Hila Fish
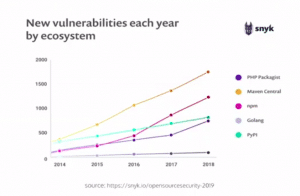
The second talk addressed a common challenge for many, selecting the right open-source project for their environment. Hila shed light on the DevOps perspective of open-source, emphasizing the importance of aligning an OSS project with your specific needs and pain points. With practical advice and insights, the talk guided attendees on how to evaluate key indicators and make informed choices, saving valuable time and resources.
Acknowledging Our Sponsors
Before we continue, we’d like to extend our heartfelt gratitude to our generous sponsors. Their support has been instrumental in making this conference possible. We truly appreciate their contributions, and their commitment to our community is invaluable. Thank you!
GitOps in Kubernetes with Alex Soco.
Alex’s presentation talked about a popular open-source GitOps Kubernetes Operator, ArgoCD. He explained how ArgoCD leverages the GitOps pattern to define application states through Git repositories. This simplifies Kubernetes management by automatically syncing Kubernetes manifests to target clusters, ensuring they remain in the desired state. It’s a valuable tool for streamlining Kubernetes operations.
Conclusion
As the day drew to a close, attendees not only had their minds enriched with knowledge but also their appetites satisfied with sumptuous food. The quality of the speakers left everyone looking forward to the rest of the conference. But that’s not all; the evening event promises to be a memorable one, featuring our renowned party with roulette—a fantastic opportunity for networking, relaxation, and fun.
In Berlin, we’re not just about sharing insights; we’re also about creating lasting memories. Stay tuned for more updates from the Berlin conference as we continue our journey of discovery, learning, and celebration.