Today I’ll show you a side project I’ve been working on the past month to defend my personal systems and practice shell-scripting and forwarding logs. It is just a proof-of-concept that is work in progress. I have decided to share my project, because Open Source = Open World! You can find detector here on Github.
This small project follows 3 basic goals: a) minimal b) trustable c) modular & customizable:
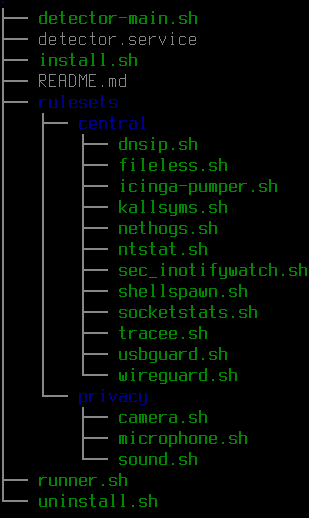
- Required Binaries for Checks: AWK, SED & GREP (en masse), Inotify-Tools, Tracee, TS, USBGuard, SocketStats, Dialog, (Nethogs)
- Just run the ./install.sh or ./uninstall.sh
- Comment or uncomment the execution of the scripts/modules in the central/privacy directories as you like
How it basically works:
– Runner: Create a 1) Systemd service with a timer, calling a 2) Watchdog with a timer, 3) calling a main (separating Operating Systems and module choices), 4) calling the modules
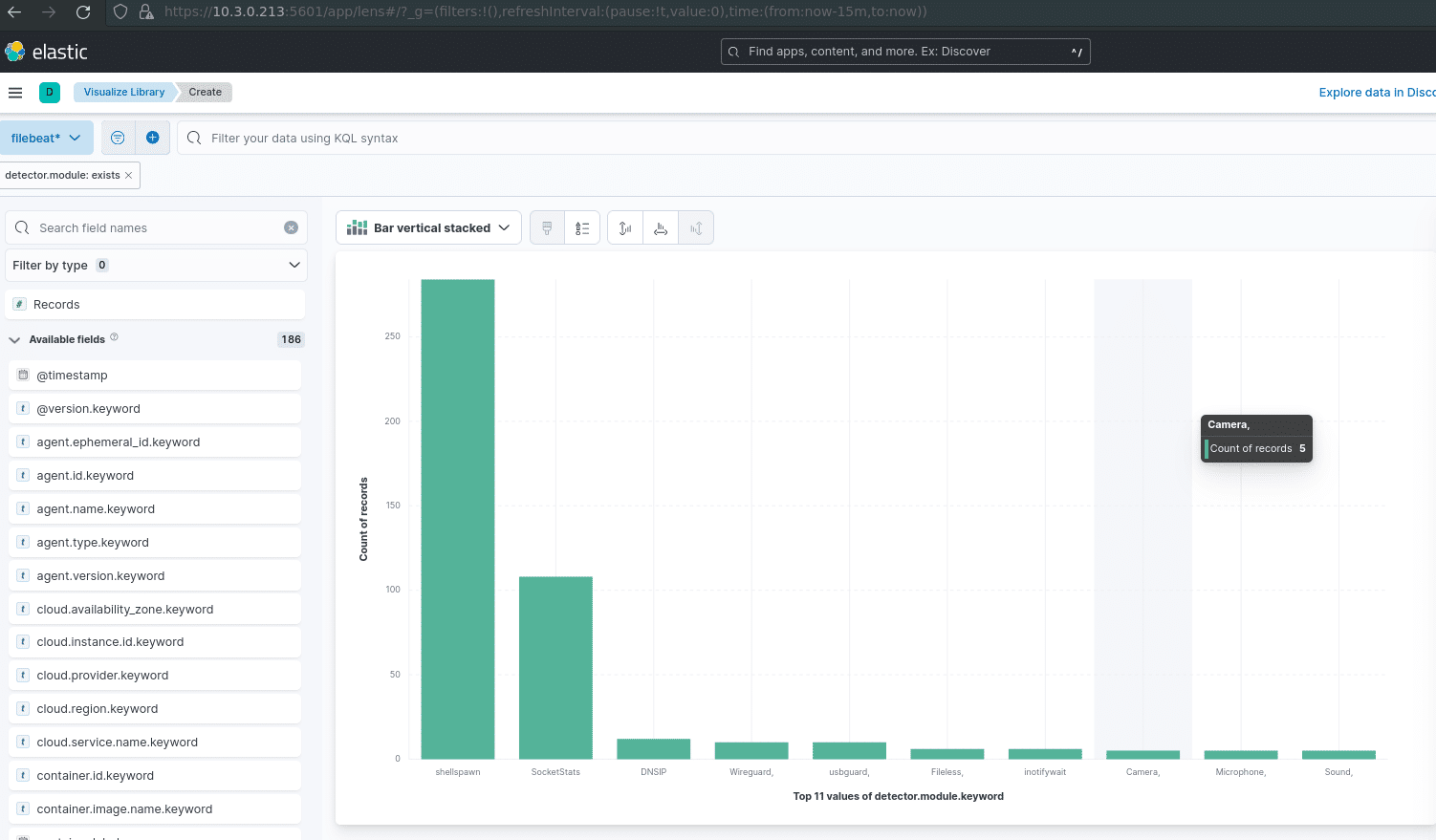
– Modules: 5) run checks 6) grep for exit codes 6) append a time-stamp 7) append a module tag (with a possible KV – filter for Logstash-Pipelines) ->> write to detecor-logfile | Optional: 9) output to Elastic (via Filebeat -> Logstash-Pipelines) 10) output to Icinga 2 (via passive-checks for more logic & free alerting)
Detector currently (2022/08/01) covers:
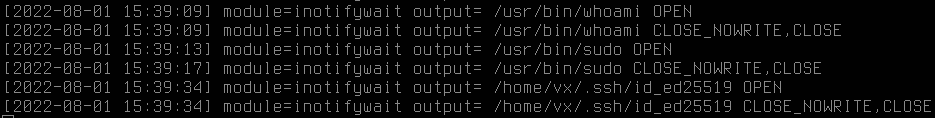
Dropping & tracking honeypots via inotifywait:
Tracking USBGuard:
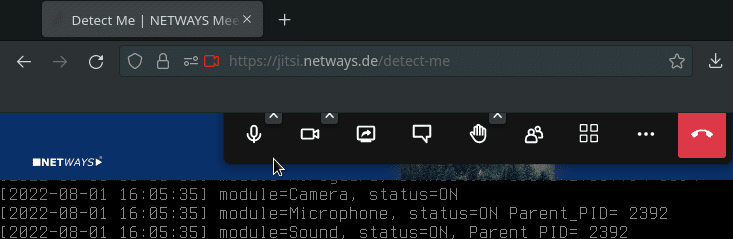
Checking Camera & Microphone Activation:
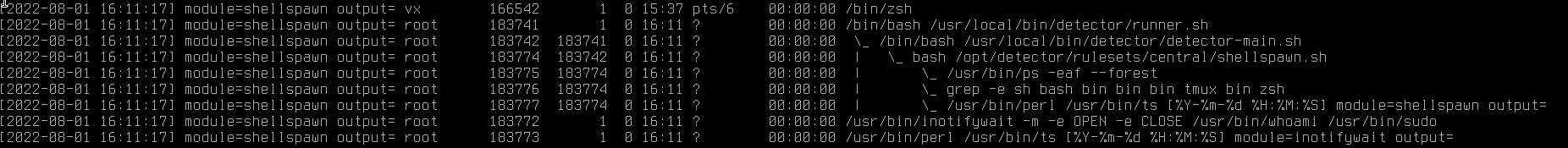
Tracking Shells and Sub-Shells:
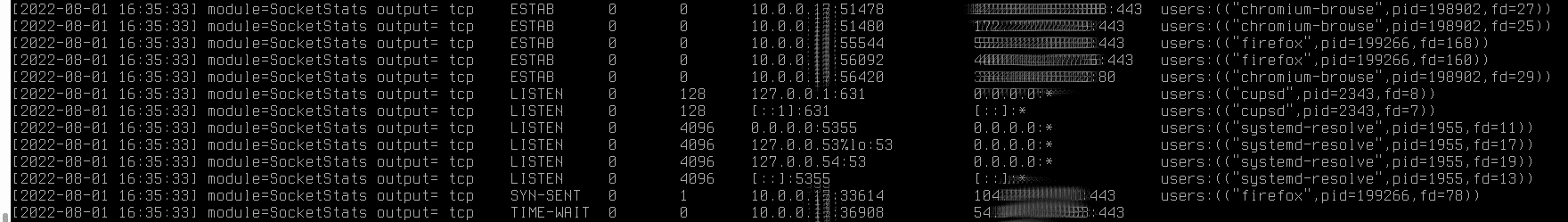
Tracking Established and Listening Sockets with their relevant Programs and PIDs, plus provided DNS-Servers and Wireguard:
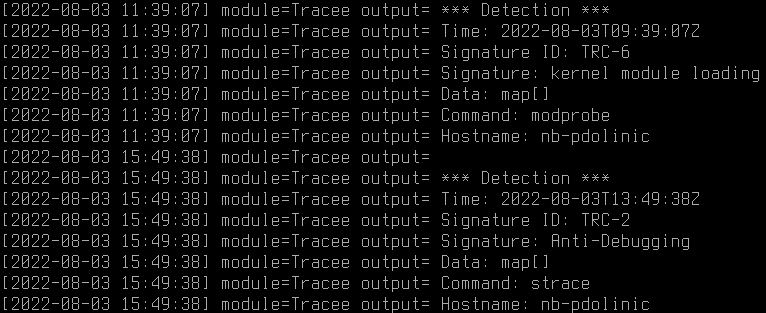
Using Tracee from Aquasecurity with 4 cool flags: TRC-2 Anti-Debugging , TRC-6 kernel module loading, TRC-7 LD_PRELOAD, TRC-15 Hooking system calls:
Tracking Kernel-Symbol counters for changes on module export tables:
Now we can be happy, but why not send it to Elastic and do some more magic there?
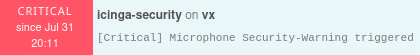
Or add even more logic and alerting via Icinga 2! (All we have to do is create a template for a passive check, apply the passive check over a (Linux)-hostgroup and set up an API-User with the “actions/process-check-result”. Our icinga-pumper.sh POC Code gets automatically executed in the $central directory, and we save ourselves the Icinga 2 agent installation, while Icinga 2 authentication happens over a certificate deployed via Nextcloud or the likes. :
TrippleCross and badbpf are some very cool offensive projects with eBPF implants I’ll try to understand and study until the next blogpost. See you by then!
If you want to learn from the people that tought me to pull such a side-project off, mostly Dirk and Thomas, then come and join us!


















0 Comments