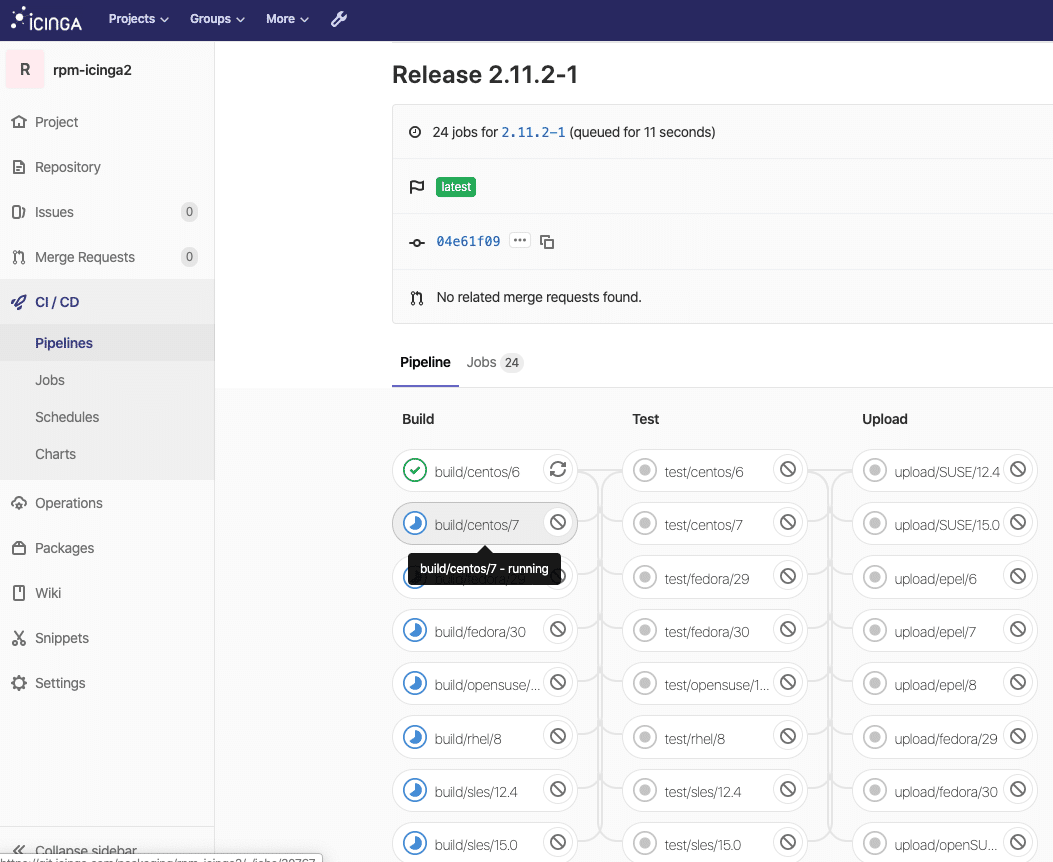
Getreu dem Motto: “you answered – we listened” hat unser NWS-Platform-Team diese Woche für unsere Kunden neue Optionen zum Erstellen von Managed Kubernetes Clustern eingeführt, die im folgenden kurz erläutert und vorgestellt werden:
1. Neue Kubernetes Versionen
Das neueste Kubernetes Major Release 1.21 ist jetzt – einen Monat nach dem offiziellem Release – auch für NWS Kunden einsatzbereit! Änderungen und Neuigkeiten findet man wie gewohnt im offiziellen Changelog.
Neben der aktuellen Version 1.21 gibt es weiterhin die Möglichkeit, Kubernetes Cluster in den Versionen 1.18, 1.19 und 1.20 zu erstellen. Die Version 1.18 ist jedoch bereits “End of Life” und deswegen nicht mehr unbedingt zu empfehlen.
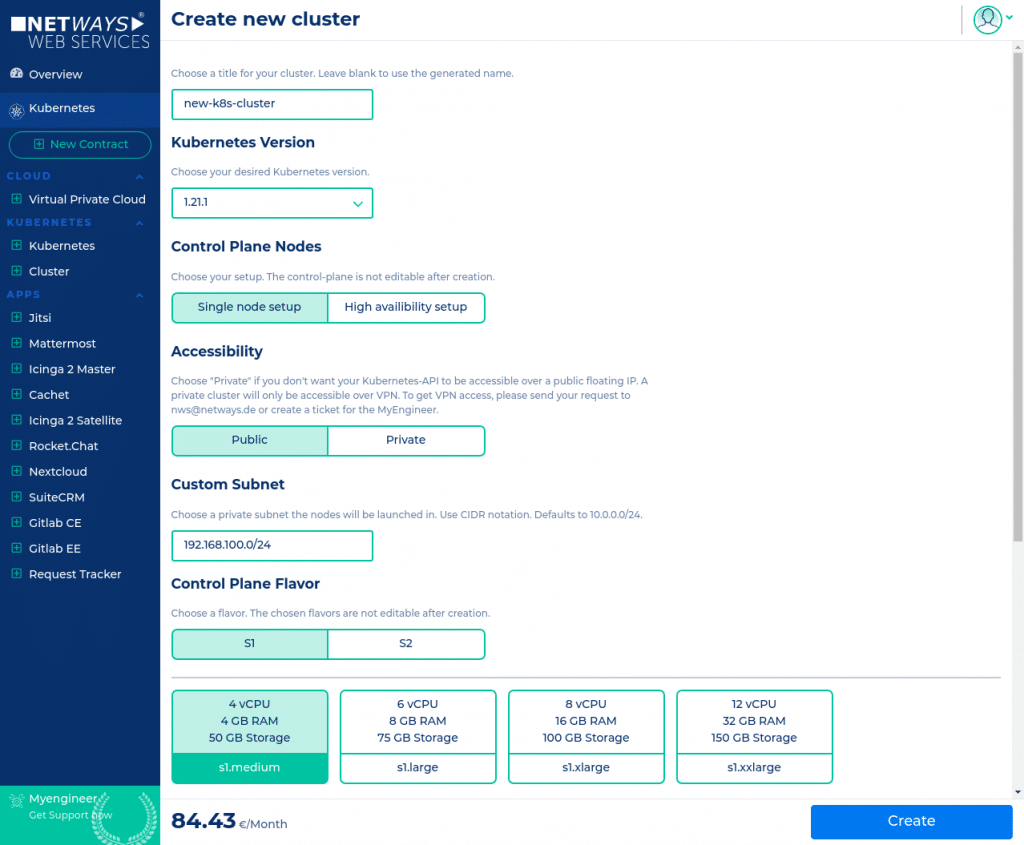
2. Private Cluster
Beim Erstellen eines Clusters kann man ab sofort zwischen einem “Private” oder einem “Public” Cluster wählen. Damit wird die Erreichbarkeit der Kubernetes-API des Clusters gesteuert. Ein privater Cluster hat nur eine interne IP und keine weitere öffentliche Floating-IP und ist dementsprechend nur von innerhalb der Kundenumgebung (OpenStack- oder Kubernetes-Projekt) erreichbar oder via VPN.
3. Individuelle Subnetze
Ebenso kann beim Erstellen eines neuen Clusters das Subnetz – in dem die Nodes kommunizieren – frei gewählt werden. Das ist insbesondere dann hilfreich, wenn man einen privaten Kubernetes Cluster per VPN mit einem bestehenden Firmennetz verbindet!
4. Rotate CA
Das Rotieren der Kubernetes CA kann jetzt über die Web-Oberfläche angestoßen werden. Es wird eine neue Cluster CA erzeugt und entsprechend neue Schlüssel und Zertifikate für Service-Accounts und Kubernetes-Nodes verteilt. Die bestehende kubeconfig-Datei des Administrators muss dann durch eine neue ausgetauscht werden.
Kubernetes Tutorials
Wer sich nochmal eine genaue Anleitung, wie man schnell und einfach sein Managed Kubernetes bei NWS aufsetzt, durchlesen möchte, der findet diese und viele weitere Kubernetes Tutorials auf unserer Website. Gerne mal vorbeischauen!

 So lässt sich das OpenStack Projekt bequem und übersichtlich über unser Dashboard zusammenstellen und einrichten. Der Punkt der Übersichtlichkeit führt mich auch gleich zu einem weiteren wichtigen Vorteil unseres OpenStack Angebots: Bezüglich der Kosten können wir ein maximales Maß an Transparenz bereitstellen. Es gibt keine undurchsichtigen Pauschalen und Gesamtpakete. Alle verwendeten Ressourcen werden stundengenau abgerechnet. Über unseren Cost Explorer siehst Du die für den Monat bereits entstanden Kosten und bekommst anhand der aktuell genutzten Ressourcen auch gleich eine Hochrechnung über die voraussichtliche Summe am Monatsende. Man hat die Kosten also zu jeder Zeit im Blick und kann im Bedarfsfall sofort reagieren. Das liegt auch daran, dass es keinerlei Vertragslaufzeiten gibt. Wird eine VM nicht mehr benötigt, kann man diese umgehend runterfahren. Am Monatsende zahlst Du dann nur den Betrag, der bis zu der Abschaltung entstanden ist. Das gibt Dir absolute Flexibilität in beide Richtungen – Du kannst schnell wachsen und, wenn nötig, Dein Setup auch direkt verkleinern.
So lässt sich das OpenStack Projekt bequem und übersichtlich über unser Dashboard zusammenstellen und einrichten. Der Punkt der Übersichtlichkeit führt mich auch gleich zu einem weiteren wichtigen Vorteil unseres OpenStack Angebots: Bezüglich der Kosten können wir ein maximales Maß an Transparenz bereitstellen. Es gibt keine undurchsichtigen Pauschalen und Gesamtpakete. Alle verwendeten Ressourcen werden stundengenau abgerechnet. Über unseren Cost Explorer siehst Du die für den Monat bereits entstanden Kosten und bekommst anhand der aktuell genutzten Ressourcen auch gleich eine Hochrechnung über die voraussichtliche Summe am Monatsende. Man hat die Kosten also zu jeder Zeit im Blick und kann im Bedarfsfall sofort reagieren. Das liegt auch daran, dass es keinerlei Vertragslaufzeiten gibt. Wird eine VM nicht mehr benötigt, kann man diese umgehend runterfahren. Am Monatsende zahlst Du dann nur den Betrag, der bis zu der Abschaltung entstanden ist. Das gibt Dir absolute Flexibilität in beide Richtungen – Du kannst schnell wachsen und, wenn nötig, Dein Setup auch direkt verkleinern.

 Vermutlich haben sich bei fast allen durch Covid-19 die Prioritäten verschoben, bei mir kam sehr schnell zu dem Thema “Ausbildung trotz 100% Home-Office aufrecht erhalten” noch ein weiteres dazu. Und zwar das Thema Online-Schulungen bzw. genauer die technische Plattform dafür, denn um andere Aspekte wie die Kommunikations- und Präsentationssoftware, Organisation, Marketing und ähnliches haben sich dankenswerterweise andere Kollegen gekümmert.
Vermutlich haben sich bei fast allen durch Covid-19 die Prioritäten verschoben, bei mir kam sehr schnell zu dem Thema “Ausbildung trotz 100% Home-Office aufrecht erhalten” noch ein weiteres dazu. Und zwar das Thema Online-Schulungen bzw. genauer die technische Plattform dafür, denn um andere Aspekte wie die Kommunikations- und Präsentationssoftware, Organisation, Marketing und ähnliches haben sich dankenswerterweise andere Kollegen gekümmert.