Es fing bereits 2015 an zu brodeln, als AWS seinen neuen SaaS-Dienst „AWS Elasticsearch Services“ veröffentlichte und später dann 2019 das Produkt OpenDistro erschien. Bei zuletzt genanntem Produkt erschließt sich mir bis heute nicht, warum ich dieses der X-Pack Basic von Elastic vorziehen sollte. So lange ich natürlich ein Elasticsearch oder den Elastic Stack nicht als SaaS-Dienst vermarkten möchte. Denn dann bleibt mir nur die bis vor kurzem verfügbare OSS-Variante, welche natürlich entsprechende Features, welche im X-Pack Basic integriert sind, vermissen lässt.
2017 auf der ElasticON in San Francisco wurde das neue offene Lizenz-Modell auf Basis der Apache-2.0-Lizenz und der daraus entstandenen OSS-Variante, so wie die Veröffentlichung einer X-Pack Basic Variante bekannt gegeben. Dieser Weg wird jetzt teilweise verlassen.
Anfang des Jahres war der Höhepunkt einer langen gerichtlichen Auseinandersetzung wohl erreicht. Elastic kündigte im Januar, wohl als letztes Mittel gegen Amazon, dass Ende der OSS mit Version Elasitc Stack 7.11 und den Wechsel zu einem dualen Lizenzmodell aus Server Side Public License (SSPL, wie z.b MongoDB) oder Elastic-Lizenz an. Amazon reagierte darauf und brachte die Community zum kochen, dass Ergebnis ist der Fork von Amazon „OpenSearch“, welcher auf Elastic Stack v 7.10 aufbaut.
Jetzt wollen wir aber mal alles im Detail betrachten und wie es weitergeht.
Spieler 1: Elastic
- Weiterhin offen und Kostenlos
- Ankündigung als Teil II zu dem Artikel aus 2018
- Warum dieser Schritt dere Liizenzännderung
- Offizielle Erklärung zum Lizenzmodell
- FAQ zum neuen Lizenzmodell
Was bedeutet dies jetzt für die Nutzer von Elastic Stack Produkten (IMHO):
- Die OSS Varianten welche Elasticsearch, Kibana und Beats unter APLv2 frei nutzbar und auch als SaaS-Dienst verkaufbar machten wurden abgekündigt mit Version 7.10
- Die X-Pack Basic bleibt bestehen und ist weiterhin frei Verfügbar und nutzbar mit allen Features, die darin enthalten sind
- Lediglich die Vermarktung des Elastic Stack als SaaS-Dienst ist nicht mehr möglich
IMHO: Bisher für mich in der Wertung alles noch kein Beinbruch und viele Reaktionen unverständlich, denn von irgendwas muss ja als Firma gelebt werden. Zudem darf man nicht vergessen, dass mit den Werkzeugen des Elastic Stack, hervorragende Standards für ein modernes Event und Informations-Managment geschaffen wurden.
Was mich aber wirklich aufregt an der ganzen Sache ist der Fakt, dass mit der Filebeat Version 7.13, die Beats nur noch mit Elasticsearch und Kibana mit Versionen ältere als 7.10 sprich 7.11 zusammen spielen. Breaking Change lesen hier.
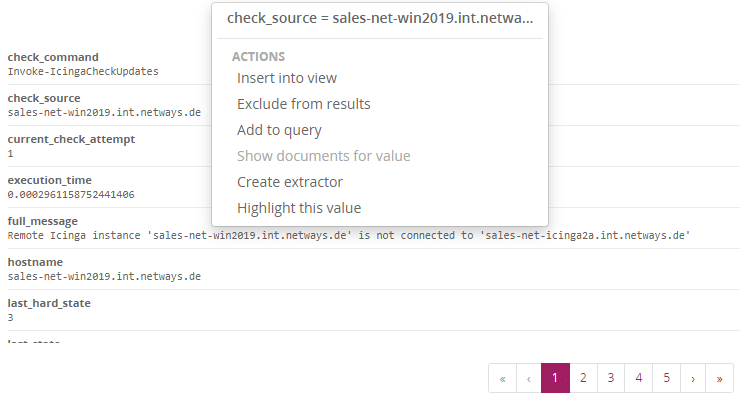
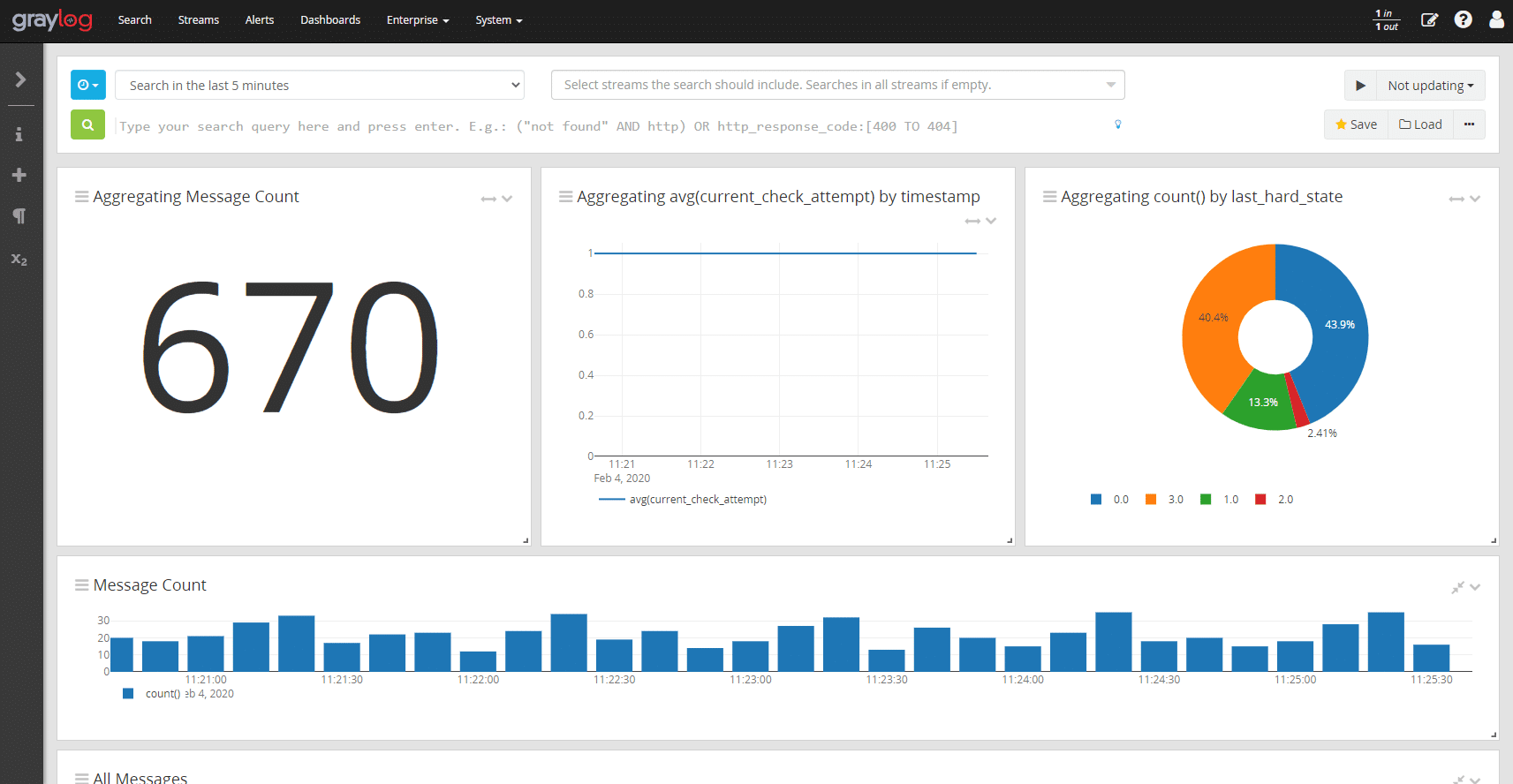
Dies könnte es schwierig machen die aktuellen Beats bzw. Filebeat mit anderen Werkzeugen wie z.B. Graylog zu nutzen. Aber dies werden wir für euch testen und berichten.
Spieler 2: OpenSearch
Als Antwort auf die Veränderungen des Elastic Stack wurde die Community unter anderem um AWS OpenDistro laut und es brodelte weiter bis es zum Ausbruch kam und Amazon AWS den Fork von Elastic Stack OSS 7.10 bekannt gab. Dies zunächst in Form von „OpenSearch“ als Fork von Elasticsearch und OpenDashboard als Fork von Kibana. Beide kommen bereits mit einer Vielzahl an Plugins und Integrationen, wie Sie es im Elastic Stack gibt. Hier ist schon mal ein guter Grundstock vorhanden.
Am 25.5.2021 wurde die Roadmap veröffentlicht welche besagt, dass der aktuelle RC1 am 12.07.2021 als v1.0 veröffentlicht wird.
Jetzt wollen wir aber auch die Gegenseite Stellung beziehen lassen:
- Am 21.01.2021 wurde der Fork ausgerufen und der heldenhafte Einsatz für ein ehrliches und quelloffenes Elasticsearch erklärt
- Am 12.04.2021 wurde der Fork „OpenSearch“ öffentlich vorgestellt und gestartet.
Was bedeutet das für neue Nutzer oder Nutzer von OpenDistro oder von Nutzern des AWS Saas-Dienstes (IMHO):
- Abwarten ist hier angesagt der RC1 welchen wir uns natürlich für euch bereits ansehen und auch demnächst vorstellen werden ist „nur“ ein RC.
- Nutzer von OpenDistro sollten mit der Veröffentlichung von Version 1.0 umsteigen. Dennn OpenDistro wird mit Version 1.13 eingestellt!
- „AWS Elasticsearch Service“ Nutzer müssen nicht bangen.
- Denn es gibt eine Abwärts-Kompatibilität zu Elasticsearch und Kibana 7.10.2 wie hier besagt und in den FAQs beschrieben.
- Diese Abwärts-Kompatibilität bedeutet es ist auch von Elasticsearch-OSS 7.10 oder gar 6.0 auf OpenSearch möglich.
- Wer Elasticsearch als SaaS-Dienst oder in SaaS-Dienste oder ähnlichen Produkt-Formaten verwenden will muss auf OpenSearch setzen (oder einfach Solr nutzen)
Abschließend bleibt zu sagen…
Nun liebe Lesenden ich weiss, dass war jetzt alles nichts technisches. Aber wir sind bereits den RC1 fleißig für euch am Testen und werden euch so bald es passt davon berichten. Vielleicht sogar passend zur Veröffentlichung von Version 1.0 am 12.07.2021?
Wer bisher auf den „alt“ bewährten Elastic Stack setzen möchte, kann dies in der Zukunft natürlich gerne weiterhin tun. Zu mal auch abzuwarten bleibt, wie es sich bei einer Vielzahl von Anwendungen welche auf Elasticsearch als Speicher setzen, wie z.B Graylog mit der Integration verhält.
IMHO: Für mich ist klar Amazon in Form von AWS hat, dies bewusst provoziert und ist nicht der faire Spieler in dieser Partie (gewesen). Denn wenn man durchs Leben geht sollte es immer gelten ….
Bei allem, was wir denken, sagen oder tun, sollten wir uns fragen:
1. Ist es wahr?
2. Ist es fair für alle Beteiligten?
3. Wird es Freundschaft und guten Willen fördern?
4. Wird es dem Wohl aller Beteiligten dienen?”
Wer zu den oben erwähnten Themen und Werkzeugen Unterstützung benötigt, darf sich natürlich gerne von uns helfen lassen und bei den Kollegen von Sales nach einem/r Kollegen/Kollegin von Professional Services fragen. Oder in einer unserer Schulungen zu Graylog oder dem Elastic Stack lernen, wie mit den Werkzeugen in der Produktion umgegangen wird.

 Mit Graylog 3.2 haben die Kollegen von
Mit Graylog 3.2 haben die Kollegen von  Optimierte Such-Konfiguration (ENTERPRISE)
Optimierte Such-Konfiguration (ENTERPRISE)