
This is where smart cards come in. A smart card stores certificates (such as your SSH key) and provides functionality for operating on those certificates (e.g. using their private key to sign or decrypt data). Smart cards come in various form factors: credit cards, SIM cards, etc. – which commonly require a separate card reader in order to be usable. However, there are also USB devices which implement all the usual smart card features in addition to other security features (e.g. requiring the user to press a key on the device before an authentication request is signed).
One such device is the Yubikey 4 which I’m personally using for SSH authentication.
The first step towards using a new Yubikey for SSH authentication is enabling the OpenPGP applet on it:
$ ykpersonalize -m82
I already had a PGP key, however in order to use it for authentication I had to create an additional subkey for the key usage type „authentication“. Here’s how that can be done:
$ gpg --edit-key --expert info@example.org gpg (GnuPG) 2.1.23; Copyright (C) 2017 Free Software Foundation, Inc. This is free software: you are free to change and redistribute it. There is NO WARRANTY, to the extent permitted by law. Secret key is available. sec rsa2048/42330DF1CA650A40 created: 2017-08-24 expires: never usage: SC trust: ultimate validity: ultimate ssb rsa2048/56D8D1BBE7E720DB created: 2017-08-24 expires: never usage: E [ultimate] (1). NETWAYS Blog <info@example.org> gpg> addkey Please select what kind of key you want: (3) DSA (sign only) (4) RSA (sign only) (5) Elgamal (encrypt only) (6) RSA (encrypt only) (7) DSA (set your own capabilities) (8) RSA (set your own capabilities) (10) ECC (sign only) (11) ECC (set your own capabilities) (12) ECC (encrypt only) (13) Existing key Your selection? 8 Possible actions for a RSA key: Sign Encrypt Authenticate Current allowed actions: Sign Encrypt (S) Toggle the sign capability (E) Toggle the encrypt capability (A) Toggle the authenticate capability (Q) Finished Your selection? s Possible actions for a RSA key: Sign Encrypt Authenticate Current allowed actions: Encrypt (S) Toggle the sign capability (E) Toggle the encrypt capability (A) Toggle the authenticate capability (Q) Finished Your selection? e Possible actions for a RSA key: Sign Encrypt Authenticate Current allowed actions: (S) Toggle the sign capability (E) Toggle the encrypt capability (A) Toggle the authenticate capability (Q) Finished Your selection? a Possible actions for a RSA key: Sign Encrypt Authenticate Current allowed actions: Authenticate (S) Toggle the sign capability (E) Toggle the encrypt capability (A) Toggle the authenticate capability (Q) Finished Your selection? q RSA keys may be between 1024 and 4096 bits long. What keysize do you want? (2048) Requested keysize is 2048 bits Please specify how long the key should be valid. 0 = key does not expire = key expires in n days w = key expires in n weeks m = key expires in n months y = key expires in n years Key is valid for? (0) Key does not expire at all Is this correct? (y/N) y Really create? (y/N) y We need to generate a lot of random bytes. It is a good idea to perform some other action (type on the keyboard, move the mouse, utilize the disks) during the prime generation; this gives the random number generator a better chance to gain enough entropy. sec rsa2048/42330DF1CA650A40 created: 2017-08-24 expires: never usage: SC trust: ultimate validity: ultimate ssb rsa2048/56D8D1BBE7E720DB created: 2017-08-24 expires: never usage: E ssb rsa2048/5F43E49ED794BDEF created: 2017-08-24 expires: never usage: A [ultimate] (1). NETWAYS Blog <info@example.org> gpg> save
Now that we’ve created a new subkey we can move its private key part to the smart card:
$ gpg --edit-key --expert info@example.org gpg (GnuPG) 2.1.23; Copyright (C) 2017 Free Software Foundation, Inc. This is free software: you are free to change and redistribute it. There is NO WARRANTY, to the extent permitted by law. Secret key is available. sec rsa2048/42330DF1CA650A40 created: 2017-08-24 expires: never usage: SC trust: ultimate validity: ultimate ssb rsa2048/56D8D1BBE7E720DB created: 2017-08-24 expires: never usage: E ssb rsa2048/5F43E49ED794BDEF created: 2017-08-24 expires: never usage: A [ultimate] (1). NETWAYS Blog <info@example.org> gpg> toggle sec rsa2048/42330DF1CA650A40 created: 2017-08-24 expires: never usage: SC trust: ultimate validity: ultimate ssb rsa2048/56D8D1BBE7E720DB created: 2017-08-24 expires: never usage: E ssb rsa2048/5F43E49ED794BDEF created: 2017-08-24 expires: never usage: A [ultimate] (1). NETWAYS Blog <info@example.org> gpg> key 2 sec rsa2048/42330DF1CA650A40 created: 2017-08-24 expires: never usage: SC trust: ultimate validity: ultimate ssb rsa2048/56D8D1BBE7E720DB created: 2017-08-24 expires: never usage: E ssb* rsa2048/5F43E49ED794BDEF created: 2017-08-24 expires: never usage: A [ultimate] (1). NETWAYS Blog <info@example.org> gpg> keytocard Please select where to store the key: (3) Authentication key Your selection? 3 gpg> quit Save changes? (y/N) y
The Yubikey 4 has three key slots which can be used for storing RSA keys with up to 4096 bits each. This might be an excellent opportunity to also move your signing and encryption key to your smart card – assuming you have an encrypted backup somewhere in case you lose access to your Yubikey.
The last step involves replacing ssh-agent with gpg-agent. This allows your SSH client to use your PGP certificates (including the authentication subkey we just created). In addition to that gpg-agent also supports regular SSH keys which might be useful if you have more than one SSH key and only plan to migrate one of them to your Yubikey:
I had to add the following snippet to my .profile file to start gpg-agent instead of ssh-agent:
[ -f ~/.gpg-agent-info ] && source ~/.gpg-agent-info
if [ -S "${GPG_AGENT_INFO%%:*}" ]; then
export GPG_AGENT_INFO
export SSH_AUTH_SOCK
export SSH_AGENT_PID
else
eval $(gpg-agent --daemon --write-env-file ~/.gpg-agent-info)
fi
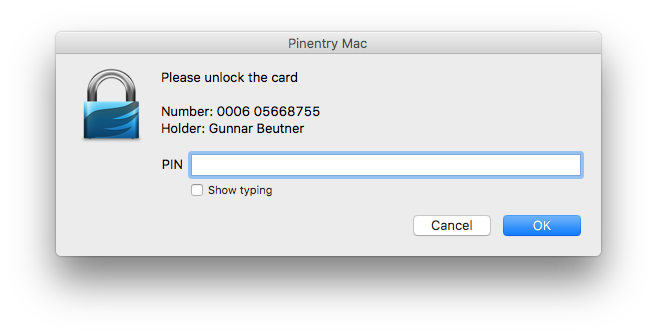
And here’s OpenSSH prompting me for my smart card and PIN:
And that’s how you can literally put your PGP key on your keychain. 🙂


















0 Kommentare